SecurityUsers of iOS devices should be on alert after the arrival of what looks like the first Trojan Horse malware developed for Apple’s mobile operating system. According to a post by Palo Alto Networks, this malware—which is known as AceDeceiver—is unique among other iOS threats…
April 4, 2016 •
3 min read
SecurityIf your employer gave you an iPhone when they hired or promoted you, then they are free to track what you do with that phone. This statement has always been true and is one of the top reasons not to send any nasty messages about…
March 28, 2016 •
2 min read
SecurityIf you’ve recently downloaded InstaCare – Who cares with me? or the similarly-named Who Cares With Me – InstaDetector, you might want to double-check the security of your Instagram account. The trojan horses, which were also being distributed in the Google Play…
March 22, 2016 •
5 min read
SecurityAll along, Apple’s biggest argument in their case against the FBI has been one of slippery slopes and escalation. The FBI wants Apple to create software that would allow them to unlock the San Bernardino shooter’s iPhone. Apple says that, once such a backdoor tool…
March 21, 2016 •
3 min read
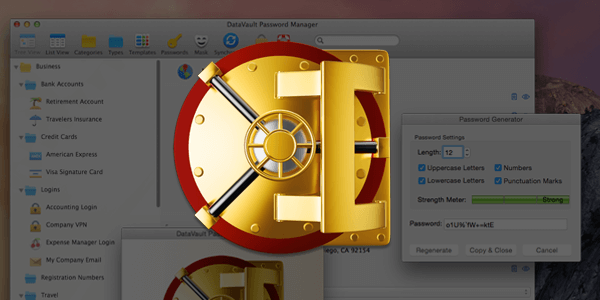
SecurityAvailable for $9.99 from the Mac App Store, the DataVault Password Manager from Ascendo is a robust password management application that is worth the modest price of admission. The program allows you to store passwords, login details, credit card information, membership information, insurance details, vehicle…
March 18, 2016 •
5 min read
SecurityCould you be rendering your Mac vulnerable to cyberattacks, just by running several popular applications? That’s the contention being made by security researchers, according to a recent report from Ars Technica. The report highlights popular BitTorrent downloading program uTorrent and screen-cropping video software Camtasia among…
March 16, 2016 •
3 min read
SecurityAnother day, another Mac malware threat to be aware of. The latest threat comes in the form of typosquatters, who are targeting make users who accidentally mistype URLs while browsing the web. According to a post written by Tom Spring on Threatpost, the Kaspersky Lab…
March 15, 2016 •
2 min read
SecurityLast year, the spyware developer Hacking Team seemed to go down in flames after a massive internal leak exposed the company’s dirty secrets for the world to see. Prior to that occurrence, the Milan-based firm had been in operation since 2003, selling products to governments,…
March 14, 2016 •
3 min read
SecurityFor weeks, Apple and the FBI have been arguing with one another over matters of privacy, cybersecurity, and national security. In February, the FBI issued a court order demanding that Apple help them break the iPhone’s security measures. Specifically, the government wants Apple to write…
March 10, 2016 •
2 min read
SecurityIn an age where wireless internet is available just about everywhere, the wired Ethernet protocol may well be a technology of the past. If you were using an Ethernet port on a Mac computer recently, you might have even noticed that it stopped working entirely….
March 10, 2016 •
2 min read
SecurityRansomware, as its name implies, is a type of malware that tries to extort money from computer users by holding their systems ransom. One of the newest types of malware to hit the scene, ransomware is an attractive choice for cyber criminals because it presents…
March 10, 2016 •
4 min read
SecurityCan you count on Gatekeeper, Apple’s proprietary malware blocking tool, to keep your computer safe? The jury is still out on that question, but one researcher has at least done his part to make Gatekeeper a bit more efficient. Last year, Patrick Wardle of the…
March 8, 2016 •
3 min read
SecurityBitTorrent Client Exposes Users to First Known Piece of OS X Ransomware Unlucky BitTorrent users who installed the latest version of Transmission over the weekend unwittingly exposed themselves to the first known piece of ransomware seen in the wild for OS X. According to a…
March 7, 2016 •
4 min read
SecurityWell, you could never say that Apple doesn’t take security threats seriously. Last year, a security firm called LegbaCore built one of the most serious threats yet to Mac computers. Typically, Macs have been known for having far, far fewer viruses and worms than PCs….
March 2, 2016 •
2 min read
SecurityEvery year, SplashData compiles a list of the most common and least secure passwords. In January, the company unveiled their “Worst Passwords of 2015” list. Hopefully, the feature can serve as a sobering reminder to Apple users—and frankly, to everyone—that some passwords really are plainly,…
February 22, 2016 •
3 min read
SecurityIn a recent feature covering some of the biggest hacks and data breaches of 2015, ZDNet dropped a chilling statistic: “Almost every American has been affected by at least one data breach this year.” Indeed, it was the year of the data breach, a year…
January 29, 2016 •
3 min read
SecurityDesigned exclusively for Mac OS X, and including full support for Apple’s latest release of OS X 10.11 (El Capitan), MacScan 3 provides protection against the continued growth of malware by offering advanced detection and removal of security and privacy threats. SecureMac, the leader in…
January 13, 2016 •
4 min read
SecuritySo you’ve just purchased a new Mac computer, be it a laptop or a desktop, and you can’t wait to dive in and start moving all of your files and data over to the new machine. Before you do any of that, though, there are…
December 28, 2015 •
6 min read
SecurityFor the 2021 version of this guide, covering both Intel and Apple Silicon Macs, click here. So you’ve decided to sell your old Mac, give it away to a friend or relative, or donate it to a school or nonprofit. Regardless of what you are…
December 16, 2015 •
5 min read