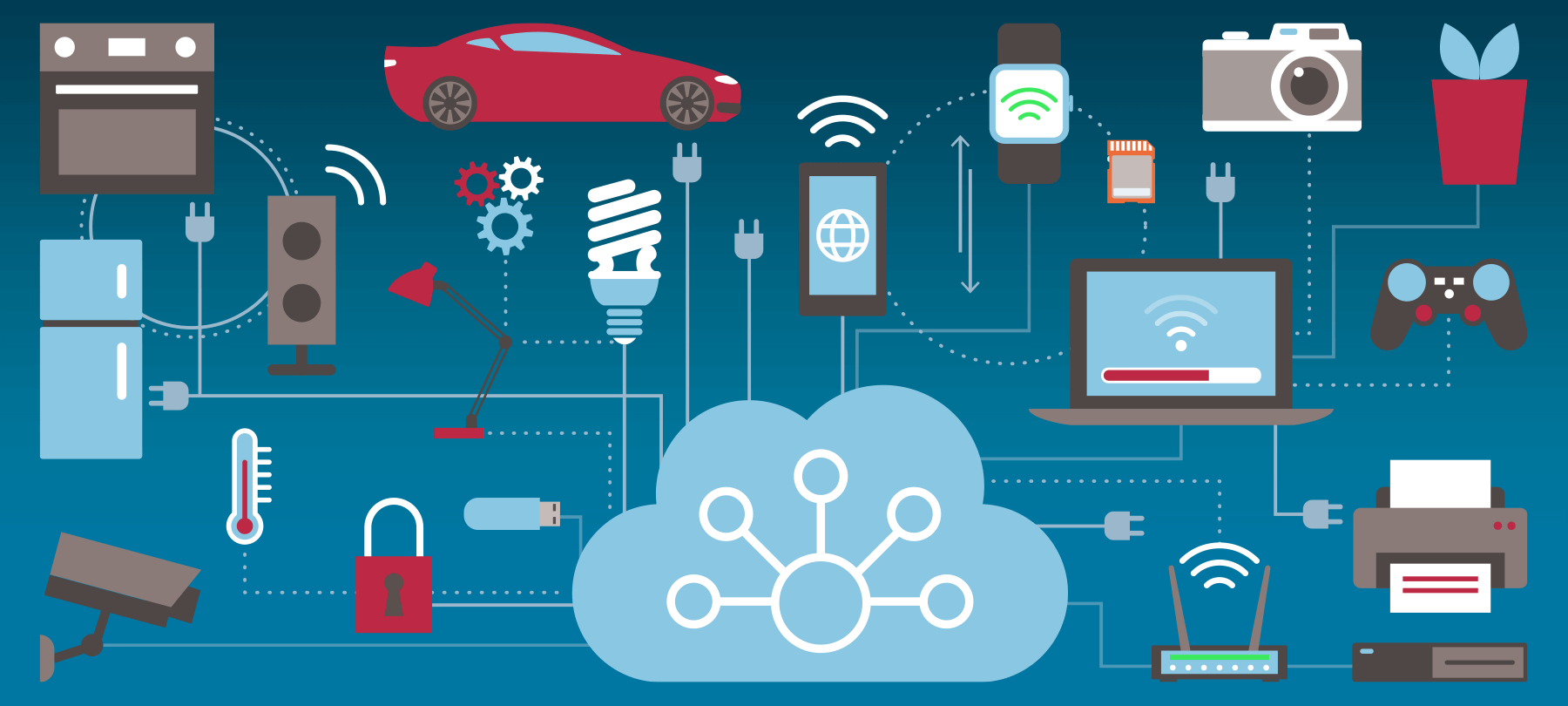
SecurityIt’s that time of year again, when kids and adults alike will soon be unwrapping presents and playing with new toys. But if you receive an Internet of Things (IoT) device as a gift, you may want to pay extra attention to the cybersecurity ramifications…
December 22, 2019 •
6 min read
SecurityIt’s that time of year again, when Santa makes his list, checks it twice and, well, you know the rest. So in the spirit of the season, we’re going to take a look at some of the top Apple stories of 2019 to see if…
December 20, 2019 •
9 min read
SecurityThis week’s Checklist topics may sound familiar, but don’t be fooled! We revisit three stories that we’ve talked about before, but which now have some updates worth discussing (spoiler: it’s not all good news!). On this week’s Checklist, it’s deja vu all over again: $20…
December 19, 2019 •
11 min read
SecurityGeorgia Weidman is a penetration tester, security researcher, writer, trainer, and entrepreneur. She is the author of a highly-regarded book which teaches the fundamentals of penetration testing, Penetration Testing: A Hands-On Introduction to Hacking, and has taught security courses and conducted advanced training sessions at…
December 17, 2019 •
13 min read
SecurityCybersecurity firm has changed with threat landscape; looks to future
December 17, 2019 •
3 min read
SecurityCupertino rolled out new features and bug fixes for all of its operating systems, so we’re going to take a look at last week’s security news broken down by OS.
December 12, 2019 •
8 min read
SecurityThe new malware sample bears similarities to the well-known AppleJeus malware, which targets cryptocurrency exchanges. AppleJeus is the product of Lazarus Group, a shadowy cybercrime organization believed by many to be linked to North Korea.
December 10, 2019 •
6 min read
SecurityOn this week’s Checklist, we’ll look at some dumb ways to buy a smartwatch. We’ll share a PSA from the FBI. And we’ll talk politics and app security by way of FaceApp.
December 6, 2019 •
13 min read
SecuritySo you’re the proud owner of a brand new Mac — wonderful! You’re no doubt eager to try out all the bells and whistles; install your favorite apps; start using your new machine. We know the feeling. But part of setting up a new macOS…
December 3, 2019 •
10 min read
SecurityThis week’s Checklist gets you ready for the seasonal shopping rush (from a cybersecurity perspective, anyway). We’ll show you how to keep safe as you shop online; what gifts you might want to avoid; and how to make sure everything arrives as planned; and what…
November 29, 2019 •
11 min read
SecurityThe holiday shopping season is almost here, and many of us are gearing up for the big sales that go with it. In particular, Black Friday and Cyber Monday are sure to be two of the busiest shopping days of 2019. But bargain hunters aren’t…
November 26, 2019 •
8 min read
SecurityA a complete guide to how to keep yourself safe during the holiday travel season. We’ll tell you what to do before you even walk out the door, how to protect yourself while you’re traveling, and what things to bear in mind when you reach your destination.
November 21, 2019 •
12 min read
SecurityThe holidays mean lots of company in and out, and travel. Follow these simple 10 tips to harden your security and keep your privacy this holiday season.
November 19, 2019 •
7 min read
SecurityHoliday travel season is almost here. And while many of us will be staying with family, friends, or in hotels, a growing number of people are making use of Airbnb to find lodging during the holidays. Airbnb rentals can be an excellent option for travellers:…
November 19, 2019 •
4 min read
SecurityOn this edition of The Checklist: Apple Mail Encryption, Now with Less Encryption!, Ransomware Revisited, and A Ring of Insecurity.
November 14, 2019 •
10 min read
SecurityPrivacy is hard to come by these days. Malicious actors, large corporations, and governments are constantly trying to look over your shoulder when you’re online. But some in the tech community are fighting back. Tools like ad blockers, no-track browsers, and VPNs can help keep…
November 13, 2019 •
8 min read
SecurityPatrick Wardle is a security researcher and software developer whose areas of expertise include macOS malware and nation-state threats. Wardle is Principal Security Researcher at Jamf and creator of the Objective-See suite of security tools. He is also the founder of the world’s premier Mac…
November 12, 2019 •
24 min read
SecurityDigital forensic analysts are the Sherlocks of cybersecurity, gathering and interpreting evidence from digital sources for use in criminal or civil court cases. While the field of digital forensics is an interesting topic in its own right, it’s also worth learning about if you’re interested…
November 11, 2019 •
8 min read
SecurityOn this week’s Checklist, we’ll talk about a privacy issue with a privacy service. We’ll look at how social engineering works in practice by examining “SIM-swapping”. And we’ll check out a high-tech hacking story that reads like something out of a Hollywood thriller. Here’s the…
November 8, 2019 •
8 min read
SecurityHigh-profile ransomware attacks on city and state governments have made national and international news in the past year. Many people are left wondering how serious the problem is—and what, if anything, can be done about it.
November 7, 2019 •
4 min read