
How to buy safe IoT gifts
Internet of Things (IoT) devices can make great gifts, but the IoT in general is notoriously insecure — and with IoT threats on the rise, that’s a real cause for concern.
November 23, 2020 • 4 min read
Internet of Things (IoT) devices can make great gifts, but the IoT in general is notoriously insecure — and with IoT threats on the rise, that’s a real cause for concern.
November 23, 2020 • 4 min read
The holiday season is here again…but this year, of course, is a little bit different. With more of us shopping from home than ever before, we’ll show you the safest ways to buy gifts online. On this Checklist, we cover: 5 best practices for 2020…
November 19, 2020 • 8 min read
The film marks its 25th anniversary this year, and we caught up with Santiago to talk about the making of Hackers; the movie’s enduring legacy, and what it means to him personally; and the relationship between technology and the arts
November 13, 2020 • 15 min read
macOS Big Sur has arrived. Or, we’ve gotten to Big Sur. Whatever the case, there’s a host of new privacy and security features in the Mac’s latest operating system. We’re talking over some of them with SecureMac’s Nick Leon on Checklist 207.
November 12, 2020 • 8 min read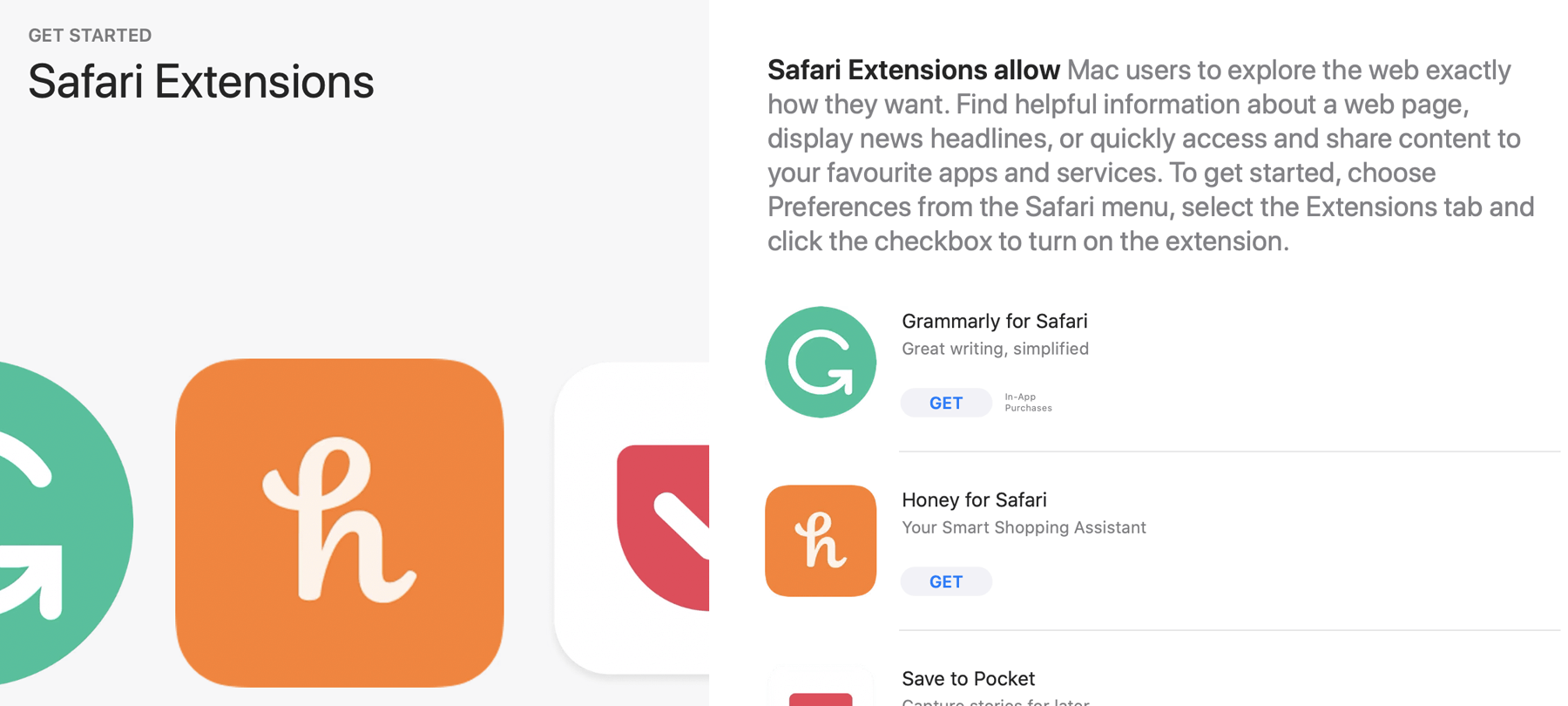
We browser extensions that function as digital shopping assistants are becoming increasingly popular, but like any piece of software, shopping extensions have potential security ramifications.
November 12, 2020 • 5 min read
Apple just held its final Special Event of the year, aptly called “One More Thing”. This fall’s previous events had focused on the new 5G iPhones and the latest iPad and Apple Watch models.
November 11, 2020 • 5 min read
Apple has just updated all of its OSes. These updates include critical security patches for vulnerabilities that have been exploited in the wild.
November 6, 2020 • 3 min read
This week on the Checklist, we’ll look at why some analysts think Apple could be gearing up to challenge Google’s search supremacy. We’ll discuss: Why people think Apple is getting into search, and What an Apple search engine could mean for privacy.
November 5, 2020 • 6 min read
The web is abuzz with rumors that Apple is poised to challenge Google’s search supremacy. In this short article, we’ll tell you why people think Cupertino may be building a search engine of its own, and say what it could mean for the future of…
October 30, 2020 • 4 min read
This week on the Checklist, we’ll cover two timely topics: cyberattacks on hospitals, and a voting contingency plan.
October 29, 2020 • 4 min read
Voters in several U.S. states have received threatening emails telling them to vote for incumbent presidential candidate Donald Trump, and vowing to “come after” them if they do not comply. U.S. officials now say that Iran was behind the emails, and that their goal was…
October 23, 2020 • 7 min read
The 2020 U.S. elections are just days away, and cybercriminals — some motivated by politics, others by financial gain — are stepping up their attacks. We’ll let you know what’s happening on this edition of the Checklist. Voter intimidation emails attributed to Iran We’ve talked…
October 22, 2020 • 8 min read
Security researchers have just announced the discovery of Android and macOS variants of GravityRAT, a Windows spyware threat that’s been around since at least 2016.
October 20, 2020 • 4 min read
On this week’s Checklist, we’ll cover: How Macs are perceived in the enterpriseAn addendum to last week’s T2 storyA checklist of security tips from the NCSA Survey says… Do you feel like your Mac is the best choice for security? You’re not alone. A recent…
October 15, 2020 • 10 min read
Tuesday’s Apple Special Event introduced the iPhone 12 line and some cool new accessories as well. Here’s an overview of the new and upcoming product releases announced at the event: iPhone 12 and iPhone 12 mini The look of the new iPhone is reminiscent of…
October 14, 2020 • 5 min read
Amid growing concern about foreign interference in the November elections, military hackers at the United States Cyber Command have started attacking the Trickbot botnet. In this short article, we’ll tell you what’s happening and why it matters for the elections. What is the Trickbot botnet?…
October 12, 2020 • 4 min read
The annual Virus Bulletin security conference was held last week; as has been the case with so many other events this year, the proceedings were fully remote, leading the organizers to call the 2020 instalment of the conference “VB2020 localhost”.
October 8, 2020 • 7 min read
This week’s big news: an “unpatchable” hardware vulnerability affecting Apple’s T2 security chip! But how serious is it, really? We spoke with Mac security expert Patrick Wardle to separate the facts from the clickbait headlines. We’ll cover: the technical backgroundwho’s impacted (and what they can…
October 8, 2020 • 5 min read
An unnamed U.S. federal agency has been breached, according to a recent report by the Cybersecurity and Infrastructure Security Agency (CISA), and third-party analysts now believe that Fancy Bear, the notorious Russian Advanced Persistent Threat (APT) group, is the likely culprit. In this short article,…
October 6, 2020 • 6 min read
In this short article, we’ll introduce you to this emerging phenomenon, tell you how it works, and offer some thoughts about the future of privacy.
October 5, 2020 • 6 min read