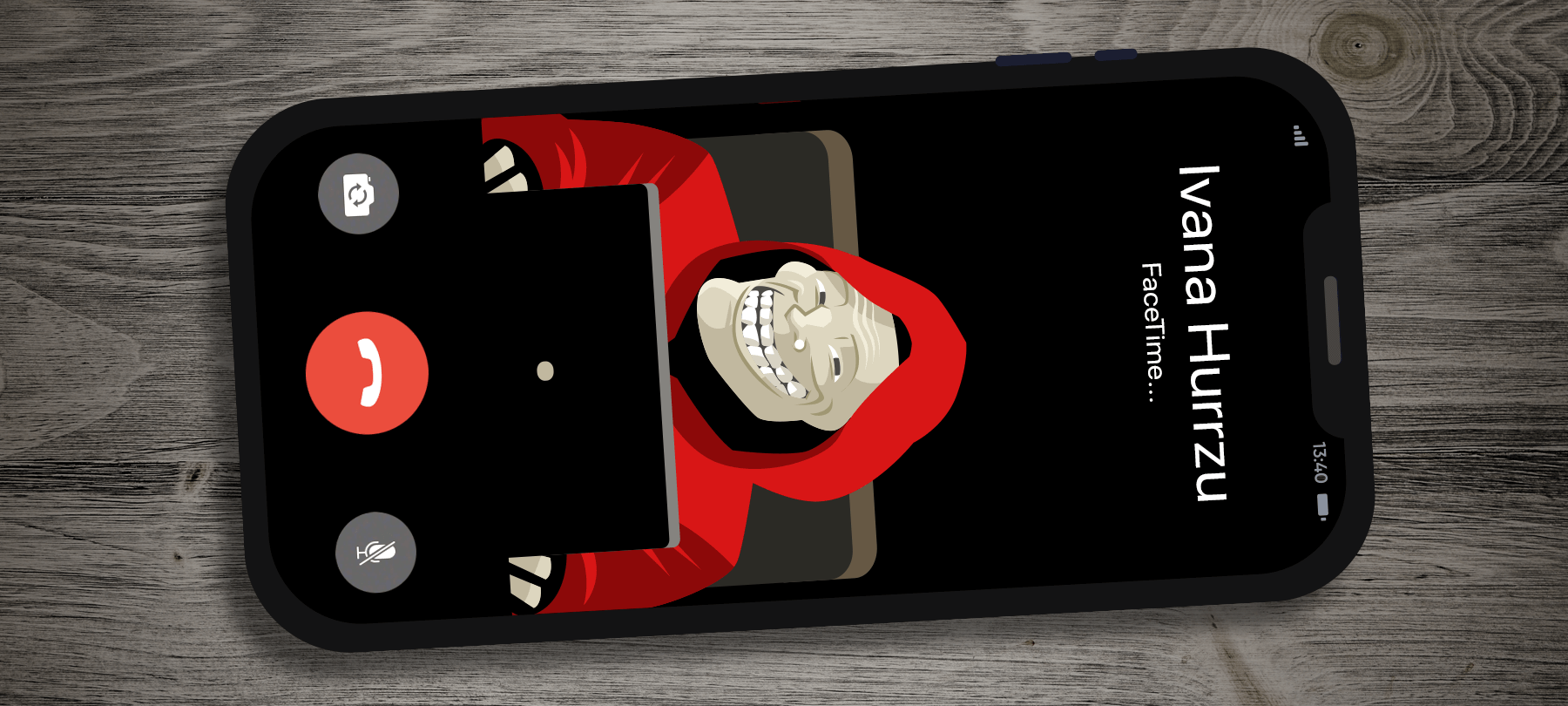
Newly-Discovered Bug in Group FaceTime Inadvertently Allows Eavesdropping
When Apple debuted iOS 12.1 late last year, one of the flagship additions to the system was Group FaceTime. This long-requested feature allows multiple users to enjoy simultaneous face-to-face video chat through FaceTime. However, in the wake of a serious flaw in Group FaceTime that was disclosed this past week, the feature is currently inaccessible on all iOS devices.
At issue is the potential risk for spying on the audio (and in some cases, video) feeds from a phone targeted through the flaw. Unlike many iOS bugs, this one does not require a convoluted series of steps or an awkward sequence of button presses. In fact, all signs point to a teenager making the original discovery of the flaw about a week before its widespread recognition.
To exploit the bug, all one has to do is initiate a FaceTime call and, before the recipient answers, add oneself to the call as an additional user. This step provides the user’s own phone with the option to accept the call. If they do, the user will now be able to hear everything being said near the microphone of the target device.
The good news is that this is not (initially) a silent bug; that is, it is not possible to trigger the flaw and eavesdrop through the target phone without also triggering that device’s ringer. However, that does little to mitigate the privacy and security risks posed by the ability to overhear someone without their consent, even for a few seconds at a time. Worse, if the user dismisses the FaceTime call request, it appears their phone begins transmitting the phone’s camera video feed — all while the user believes they are not in a call at all.
This is not the first time privacy flaws have been discovered in Group FaceTime. A previous issue patched in November allowed users to bypass the lock screen to explore a target’s address book without authorization. For now, Apple has chosen to shutter Group FaceTime temporarily, disabling server access for all users.
Although an extreme step, the effort demonstrates a clear commitment to minimizing risk and reducing the number of users potentially affected by individuals attempting to exploit the bug. The Cupertino tech giant has said a fix, which should close this loophole for good, will be available for download within approximately the next week. Users should take care to watch for this upcoming patch.
Check back here for updates on this story as they become available.
