Is SMS for 2FA insecure?
Twitter made headlines recently when the company announced it would no longer allow non-Twitter Blue users to enroll in SMS-based two-factor authentication (2FA), citing security concerns. But is SMS for 2FA really as insecure as some people say it is? The answer is more complex than it seems—and forces us to think more deeply about what security really is.
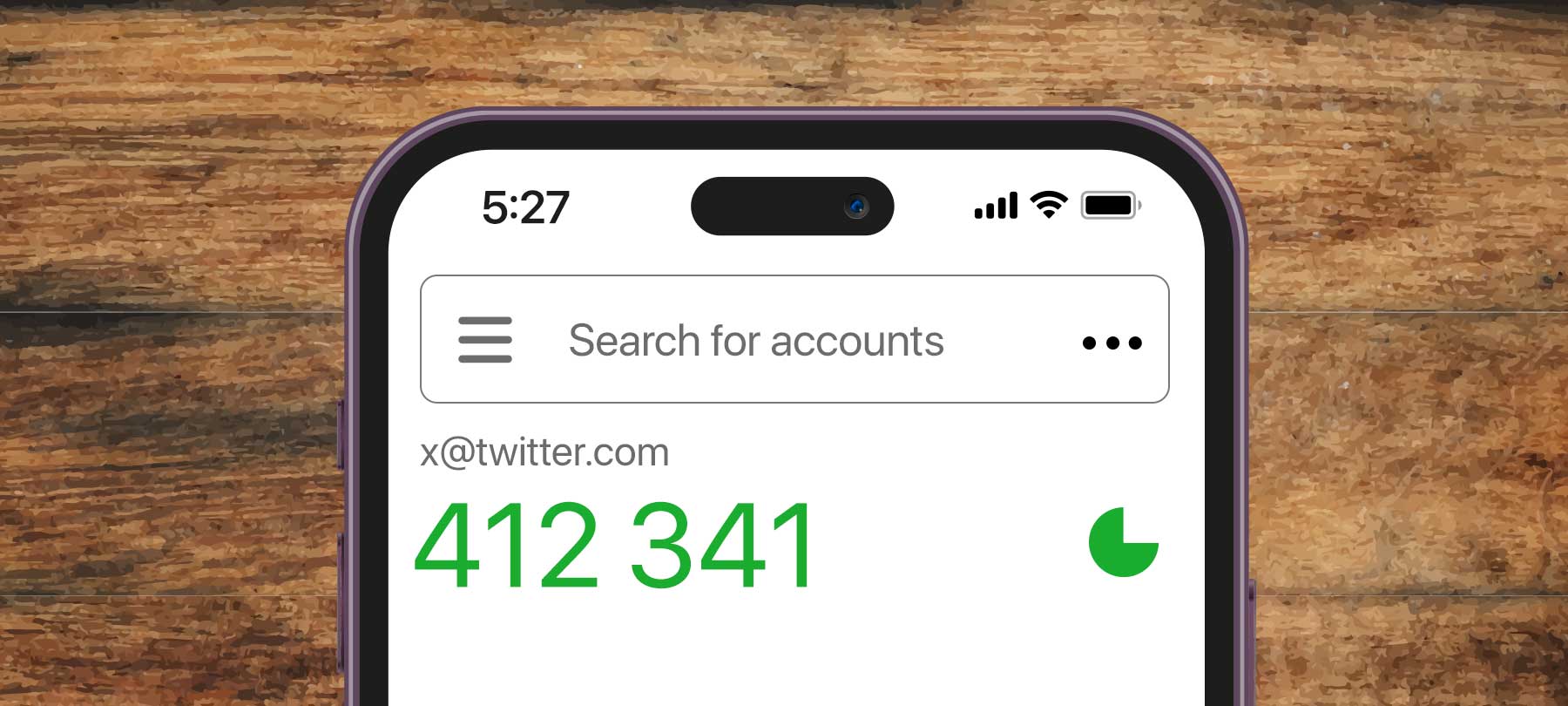
Twitter’s SMS 2FA ban
In a blog post published February 15, Twitter said that it would no longer let free-tier subscribers use SMS/text messages for 2FA. The company gave the justification that they have “seen phone-number based 2FA be used—and abused—by bad actors.”
SMS has long been regarded as a vulnerable communications protocol by security experts—but where 2FA is concerned, the biggest danger is with the possibility of SIM-swapping attacks. In a SIM swap, the bad guys trick cellular carriers into transfering a phone number to a SIM card that they control. This gives them access to the 2FA codes meant for that phone number, which lets them take over people’s accounts if they also happen to have the account password.
Twitter says that going forward, subscribers who want to protect their accounts with 2FA will need to use physical security keys or authenticator apps as their second authentication factor.
Is SMS 2FA really unsafe?
Twitter’s motivation for making this change has been called into question by many observers—both on Twitter and elsewhere. (This week’s Checklist podcast contains a more complete discussion of the issue.)
But leaving Twitter aside for a moment, is SMS for 2FA really as unsafe as some people say?
To answer that, it’s important to consider a few different things:
First, authenticator apps and physical security keys are indeed more secure than SMS for 2FA—and are the correct choice for high-risk individuals and anyone who is comfortable with technology.
Second, using SMS for 2FA is much, much more secure than using no 2FA at all.
Third, not all end users have the same level of technical ability, and while SMS text messages are already a familiar technology to almost everyone, authenticator apps and security keys are not. As Johns Hopkins University professor of cryptography Matthew Green points out:
What sets SMS 2FA apart is that it’s almost “free” from a user-effort perspective. If you own a phone, the feature is already built-in and enabled. Setup is nearly effortless. Backup is taken care of. Unfortunately none of the same things are true for HOTP/authenticator apps.
So what’s the verdict on SMS for 2FA?
From a purely objective standpoint—and when compared to more secure alternatives like app-based 2FA or security keys—it’s fair to say that SMS 2FA isn’t all that secure.
But in the real world, where many folks just aren’t going to be comfortable learning how to use an authenticator app or a physical security key, it’s equally accurate to say that SMS-based 2FA is an excellent security feature—because it’s far more secure than the alternative of “no 2FA at all.”
2FA and the goal of better security
The discussion over SMS-based 2FA takes us to the heart of what we mean by security.
We’d argue that security should be seen as an ongoing process, rather than some ideal state of affairs that can ever be achieved completely. In addition, we’d say that security isn’t a one-size-fits-all kind of thing: Different users face different threats, have different tolerances for risk, and have different levels of technical ability. What’s right for one person may be completely wrong for another.
In terms of 2FA, more technically confident users should look at switching away from SMS-based 2FA to an authenticator app or key-based 2FA.
But for users who haven’t enabled 2FA at all, and who may have a hard time with app-based 2FA, turning on SMS-based 2FA is a great first step towards better account security.
In addition, it’s possible to make SMS for 2FA a bit more secure. Most cellular carriers now allow you to protect your account with a special PIN. No one can interact with customer service or make changes to the account without that PIN, which reduces the likelihood that a SIM-swapping attack will succeed.
The bottom line is that any step that a person can take to make their account more secure is a good one!