Apple’s March 2020 Updates
Apple has just released a raft of updates, and some of them have important security and privacy implications. In this brief article, we’ll highlight some of the key points from Cupertino’s release notes and explain their significance. Then (in a sign of the times) we’ll offer a special addendum to our update guidance.
macOS 10.15.4
Version 10.15.4 of macOS patches a number of serious vulnerabilities. Related security patches were also issued to support older versions of the operating system; these were named Security Update 2020-002 Mojave and Security Update 2020-002 High Sierra.
One of the more important fixes had to do with a memory issue in the AppleGraphicsControl driver. The bug could have allowed a malicious program to execute code with kernel privileges. The word “kernel” here is the clue to the significance of the vulnerability: It refers to the code at the core of the operating system. Anything that can interfere with the operation of the kernel, or run with kernel permissions, is potentially very serious. In fact, the main reason that Apple recently did away with kernel extensions — code add-ons to the kernel created by third-party app developers for additional functionality — was the potential for security issues.
Another major bug fix — and one which took Apple the better part of a year to address — had to do with a problem in the Transparency, Consent, and Control (TCC) feature. TCC is meant to protect Mac users by letting them know what actions are being taken by apps on their systems, restricting the ability of applications to access data on other parts of the system, and helping to enforce code-signing for third-party apps. The vulnerability which was addressed in this latest macOS update could have allowed a malicious actor to bypass TCC’s code signing checks, permitting them to perform disallowed (and potentially dangerous) actions on a target system. The vulnerability was discussed in depth at last year’s Objective by the Sea 2.0 Mac security conference; for a deeper dive, have a look at our write-up of the final talk of the conference.
In addition, macOS 10.15.4 fixes problems with Bluetooth for Mac — some of which could have led to system crashes, and another one which could have permitted code execution with kernel privileges. There were also some important privacy fixes, including the correction of a bug in FaceTime which could have allowed local users to view private information, as well as a patch to a vulnerability in Call History that could have permitted a malicious application to access a user’s call records.
iOS 13.4 and iPadOS 13.4
Apple’s mobile operating systems, iOS and the closely related iPadOS, also received some important updates.
There were eight separate issues with WebKit, the web browser engine that powers Safari and all of the iOS and iPadOS web browsers. These bugs could have resulted in several potentially serious abuses, including code execution, unauthorized access to restricted memory, and cross-site scripting (XSS) attacks.
The updates also fixed a problem with Bluetooth, which has seen security and privacy issues in the past. Bluetooth is the radio-based data transfer protocol which allows our devices to detect and communicate with other nearby devices: It’s the basis of services like AirDrop, and what allows you to pair your AirPods to your iPhone. The vulnerability which Apple patched could have allowed an attacker to intercept data transmitted via Bluetooth in certain cases.
There were also three issues that affected the kernel. Two of these pertained to problems with the kernel itself — system memory issues which could have permitted code execution or unauthorized reads of restricted memory. The other bug had to do with the IOHIDFamily kernel extension, which helps the OS manage human interface tools such as touchscreens, buttons, accelerometers, and the like. Here too, a system memory issue was to blame, and could have resulted in code execution with kernel privileges.
The final patch we’ll mention fixed a problem with Messages. It didn’t address a particularly high risk vulnerability, since exploitation would have required a bad actor to have physical access to a device. But it’s still interesting from a privacy perspective, and therefore worthy of a mention: The bug could have allowed an unauthorized user to respond to the device owner’s messages — while the iOS device was locked and replies were disabled. Obviously, this isn’t something that would have affected too many users, but it’s a good reminder to pay attention to the physical side of device security, and take a “better safe than sorry” approach.
Lastly, users of older iOS devices can now update to iOS 12.4.6, though Apple says that there are no security patches in this release.
tvOS 13.4 and watchOS 6.2
If you wear an Apple Watch, or watch an Apple TV, there are some updates to these OSes that affect you.
To start with, users will be pleased to know that watchOS 6.2 and tvOS 13.4 fix many of the same kernel bugs that affected iOS and macOS, as well as the WebKit vulnerabilities mentioned above.
In addition, both OSes contain a security patch for Icons that could have allowed a malicious application to learn what other applications were running on the device — a potential privacy risk at the very least. The watchOS update also fixed a problem with sandbox restrictions in Icons, which could have led to unauthorized disclosure of media files without the proper permissions. These same issues were addressed in the iOS update, though not discussed above.
Users of Apple Watch models that are paired with iPhones running on iOS 12 can now update to watchOS 5.3.6 for compatibility with the iOS 12.4.6 update. Apple says that this update to the older version of watchOS does not contain any security fixes.
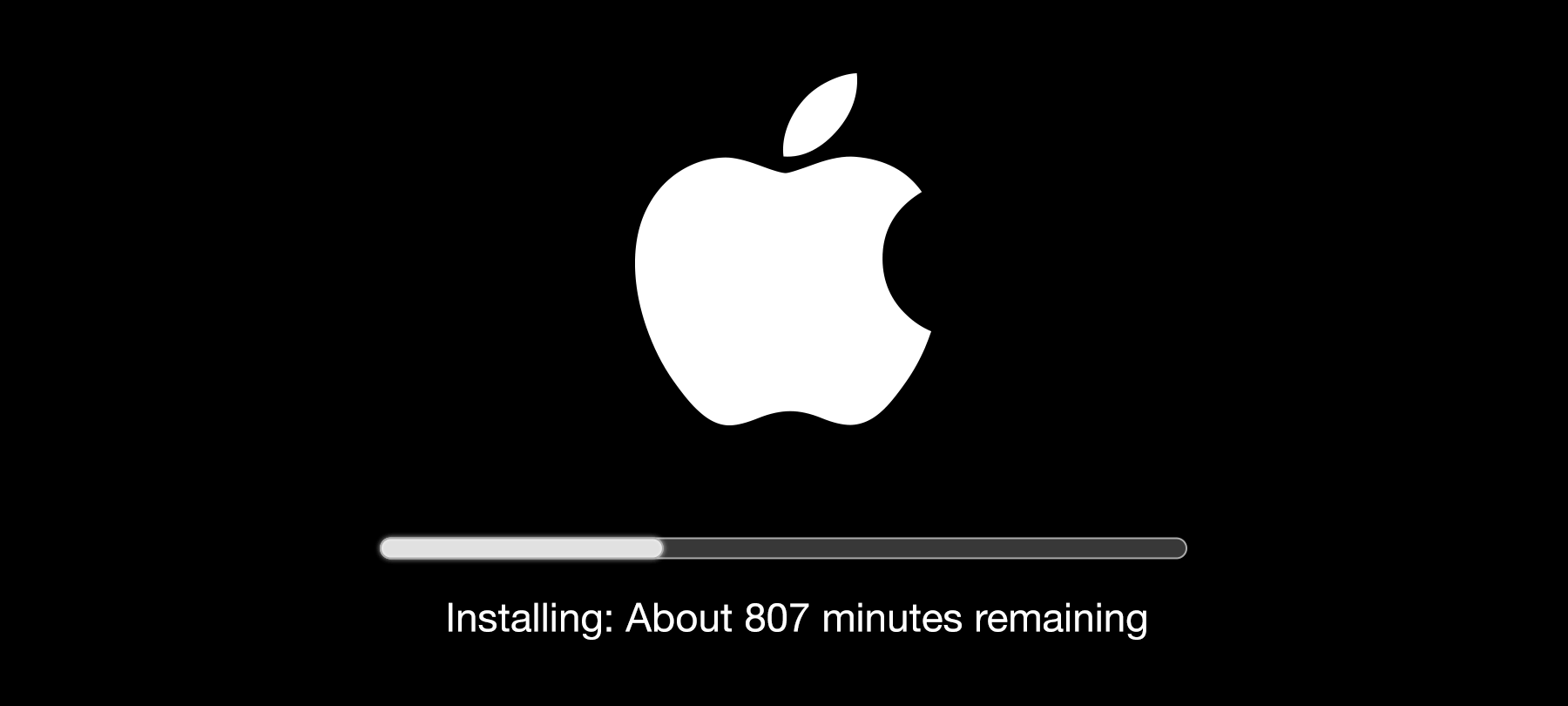
Staying safe — and backed up
As always, if you haven’t set your OS to automatically update, we recommend that you perform a manual update right away. But since many of us are working at home at the moment, and using our personal devices to do this, we’d advise taking an additional step in order to make sure that your important data is secure: Perform a full backup before running your updates. The chances of something going drastically wrong are very low, but the current situation is serious enough to warrant taking some extra precautions. While you probably won’t need your backup, you’ll be glad you have it in the unlikely event that you do!


