Initial Analysis of trojan.osx.boonana.a
The initial infection vector of the Boonana trojan is through a message on social networking sites similar to “Is this you in this video?” which includes a link to an external site. Upon clicking the link, a java applet will attempt to load in the user’s web browser.

The web browser will then prompt the user to allow content signed by an untrusted certificate to run.
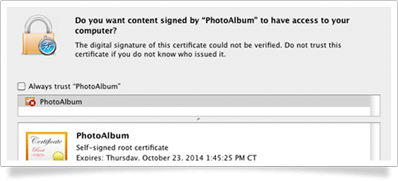
When the user accepts the certificate, the applet loads.
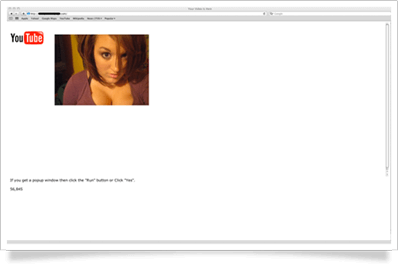
Once the applet is loaded, it displays a fake YouTube interface to simulate a “video” by displaying a random picture from a site like hotornot.com, and installs itself in a hidden directory named “.jnana” in the user’s Home folder. At this time it starts running in the background and communicating with a variety of servers.
(Side note: There appears to be a counter on the page indicating “hits” or site access, which increases with each visit. This does not indicate the number of successful infections, but this is just one of many distribution sites.)
During our testing, the malicious Java applet communicated with a Command & Control server, and presented an installer window at a random time after accessing the malicious site. This installer did not indicate that it had been downloaded from the web which indicates it is avoiding the quarantine flag typically set by programs such as Safari.
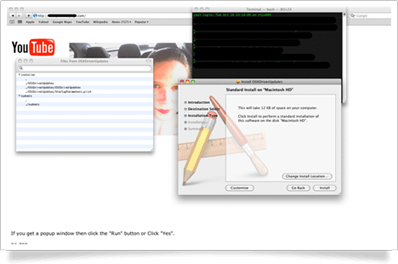
The installer does require authentication by the user to install its payload. The installer does a few things. First, it copies the contents of the hidden .jnana directory from the user’s Home folder to /var/root/.jnana/. Next, it installs a process to run at startup along with a parameters file in /Library/StartupItems/OSXDriverUpdates/. The two files are called “OSXDriverUpdates” and “StartupParameters.plist.”
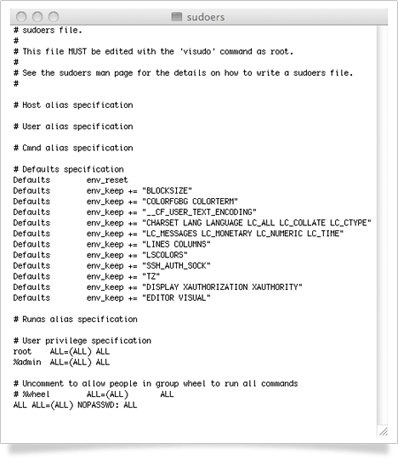
The installer also replaces the “sudoers” file in /etc with a modified copy that allows any command to be run as root without a password.
Once installed and running, the malware starts a launchd task to ensure it relaunches automatically if it exits. The launchd task is installed at ~/Library/LaunchAgents/jnana.plist.
When running, the malware attempts to connect to a number of sites, including sites to obtain the current IP address for the infected computer, as well as search portals, and other command and control servers.
Manual Removal
To manually remove the malware from infected machines, run the following terminal commands. Make sure to unload the launchd task in order to stop attempts to respawn the process:
launchctl unload -w ~/Library/LaunchAgents/jnana.plist
Make sure the java process is no longer running:
killall java
Remove the files:
sudo rm -rf ~/.jnana/
sudo rm -rf /Library/StartupItems/OSXDriverUpdates/
sudo rm -rf /var/root/.jnana/
sudo rm -rf ~/Library/LaunchAgents/jnana.plist
Finally, either manually edit the /etc/sudoers file, or restore it from a known good copy, making sure to set appropriate ownership and permissions.
Threat level
Due to the fact that the Command and Control servers for the malware are still active, gathering information such as IP addresses (most likely for control purposes), as well as the modification of the sudoers file to allow passwordless access, we maintain a threat level rating of critical for trojan.osx.boonana.a. In many cases, especially with botnets, the malware might not initially exhibit malicious behavior, but can become active at any time as the command and control servers are updated.
This post will be updated as further information becomes available.
Resources
PDF version
SecureMac’s Initial Report
Removal Tool Direct Download Page

