Security researcher Phil Stokes on the state of Mac malware
New research suggests that Mac malware is increasing exponentially — and even beginning to outpace Windows malware in terms of total threats per endpoint.
But while these findings were reported as shocking developments by the media, they come as less of a surprise to the Mac security professionals who have been watching the threat landscape evolve over the past several years.
As security researcher Phil Stokes sees it, Mac malware isn’t just increasing in prevalence. It’s also becoming more diverse — and more sophisticated.
When I first started looking at threats on macOS it was almost entirely a mixture of simple adware and browser hijackers on the one hand and “Potentially Unwanted Software” and scareware like MacKeeper and MacBooster on the other. Of course, there were occasional cases of more serious stuff, FruitFly, KeRanger and Flashback stand out … but relatively speaking, Mac users were rarely troubled by security issues.
If a user gets infected by one, they’ll very quickly end up with multiple infections.
These days, the landscape has changed in the sense that we’ve seen a consolidation and in some ways a cooperation between many of those actors, so that we now have “bundle installers” dropping adware on unsuspecting users on the one hand, and on the other the same adware redirecting users to download more bundle installers; it’s a vicious circle such that if a user gets infected by one, they’ll very quickly end up with multiple infections.
On top of that, we’ve seen many of these same actors increasingly adopt malware-like behaviour in the sense of using multiple persistence methods, more obfuscation and anti-analysis techniques, and dropping malware like Shlayer. Cryptominers have also been targeting macOS users recently, and these also use stealth techniques such as going to sleep when the user opens the Activity Monitor and hiding payloads in locations most users don’t even know exist.
As for more serious malware and threat actors, there are a number of RAT trojans around that can be used against macOS, like EvilEgg and Empyre, and we’ve also seen increased attention from so-called “nation-state actors” like the North Korean Lazarus Group and WindTail. APT groups building tools to infect macOS users is something we never really saw just a few years back.
With increasingly capable actors entering the picture, evasion and persistence techniques are growing more advanced. But also worrying are the ways in which malicious actors seem able to adapt to and overcome Apple’s own security initiatives. This new breed of bad actors is finding ways to bypass the native protections in macOS — and Apple is struggling to stop them.
It’s actually fascinating seeing threat actors adopt principles of good technical communication, albeit for the wrong reasons! It just shows how professional these operations are.
What’s particularly interesting is how easily threats get around the built-in security controls that Apple have included. Malware authors will always adapt to the challenges of their environment, so when Apple introduced things like Gatekeeper to control third-party applications, actors simply signed up for Apple developer accounts and signed their installers. Then they avoid further checks on second and third stage payloads by sidestepping both Gatekeeper and XProtect (Apple’s built-in AV scanner) by downloading payloads using CURL, which doesn’t trigger either the new Notarization checks or Gatekeeper scrutiny. Apple do revoke these signatures when they catch them, and to their credit they’ve got much more proactive about this over the last 12 months or so, but they still have to find them first.
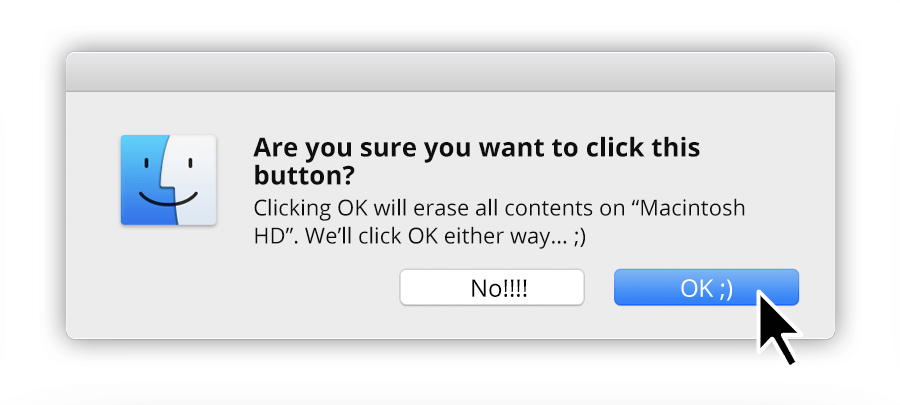
It’s also interesting how recent malware has started using shell scripts instead of Apple application bundles, and now just brazenly encourages users to override Gatekeeper with simple, effective infographics. It’s actually fascinating seeing threat actors adopt principles of good technical communication, albeit for the wrong reasons! It just shows how professional these operations are. They’re set up and run like legitimate businesses, and they employ people with the requisite skills to achieve their goals.
Clearly, much has changed in the world of macOS malware over the past several years. But despite this new reality on the ground, there is still a fundamental disconnect between people who work in security research and the wider Mac community — including technically sophisticated users — over the dangers facing the platform.
This divide can, at times, lead to mistrust. One of the authors of the research mentioned above was publicly accused of “stoking fear” by a prominent Twitter user in the tech community. It was implied that security vendors were reporting on the spike in macOS malware and exaggerating its severity as a marketing tactic. The same critic echoed a sentiment often expressed by devoted Mac users: Apple’s native protections are perfectly adequate to guard against everyday threats.
Stokes sees this kind of attitude as both behind the times and short-sighted, though perhaps understandable:
I think there’s a real disconnect between “ordinary” macOS users and the security community, and there’s a lot of distrust among the former toward the latter. I see infected Macs on a daily basis, but if you’re not involved in that side of things, if you just use your Mac in a normal, everyday kind of manner as most people do, you may never see or hear of the problems other users are experiencing. This is also true of Windows users, by the way; most have never seen any malware, but the extent of the problem is widely recognized there, whereas on Mac it’s like there’s this collective denial that the problem even exists.
A lot of longtime Mac users will tell you Macs are perfectly safe and the only “AV” you need is common sense. While common sense goes a long way in security of any kind, the view that prudence is all you need these days is partly outdated, and partly, I have to say, a bit myopic.
The data from pretty much all security vendors and indeed large organizations with Mac fleets shows that macOS attacks and infections are at an historical all-time high…
It’s outdated because it’s often based on a view of how things were 5 or 10 years ago, when the market share of Macs was so little to be of no interest to commodity adware and malware developers. The sheer number of macOS adware, PUPs and malware out there now is incomparable to how it was even just a couple of years back.
It’s also myopic in the sense that many think because something hasn’t happened to them, it isn’t happening to anyone else. But the data from pretty much all security vendors and indeed large organizations with Mac fleets shows that macOS attacks and infections are at an historical all-time high, and all the signs are that they will increase. We know from the threats that we see that bad actors are making a lot of money from macOS infections, and where there’s money to be made you’ll see increased attempts to make that money.
Public perception of the dangers facing the macOS platform may be attributable, in large part, to a lack of firsthand experience. However, some of the blame also lies with the way the media covers cybersecurity issues.
It is not uncommon to see relatively obscure or theoretical vulnerabilities discovered by security researchers and then presented in a sensationalized manner by the press as critical threats — even when there are no examples of actual, real-world exploits associated with these vulnerabilities. The “imminent danger” is, of course, forgotten as soon as the next news cycle begins, but the damage is done: Over time, readers become desensitized to reports of new Mac malware, and may begin to suspect that the risks have been exaggerated.
Yet macOS threats do exist, and they are far from theoretical dangers for the people they affect. In the view of researchers like Stokes, it is incumbent upon the security industry to provide accurate, actionable information about the more commonly seen varieties of Mac malware — even if these are not as clickworthy as their “flavor of the week” relatives.
Simply running macOS with the default security settings isn’t going to stop these threats if you’re unlucky enough to run into them.
Of course, there are always headlines about some new vulnerability or research about some novel malware from time to time, and unfortunately these stories are often blown out of proportion to grab attention, and that can have a negative consequence in terms of increasing cynicism about the motives of the entire macOS security industry.
But there’s a real duty for security vendors to also educate macOS users about the common, everyday threats that exist and which are infecting computers with impunity on a daily basis, and not just to shout about new threats and vulnerabilities that might not really be having much of an impact on users at all. At SentinelOne, we try to highlight these in regular blog posts, to explain how real, in-the-wild macOS malware works, and why simply running macOS with the default security settings isn’t going to stop these threats if you’re unlucky enough to run into them.
One party that is well aware of the increase in macOS threats is, of course, Apple. In late 2019, the company rolled out the latest version of its Mac operating system, macOS Catalina, which contained a number of new features aimed at tackling the security and privacy threats facing users: Kernel extensions were deprecated, there were several important enhancements to Gatekeeper, and app notarization was made mandatory for all third-party developers.
But not everyone is happy with the changes — and the criticisms aren’t just coming from app developers complaining that Apple has made their jobs harder. People within the Mac security community have voiced concerns that macOS may be moving too far in the direction of iOS, becoming so locked-down that independent researchers lack the access they need to help keep the system safe.
There has also been criticism — and often from “everyday” users — about Catalina’s approach to data protection. Although designed to give end users more control over what the apps on their Macs are doing, and what data and locations they can and can’t access, many are finding the constant stream of pop-ups and consent dialogs to be intrusive and unhelpful.
While Stokes is broadly appreciative of Apple’s efforts to secure its platform, he still thinks the company could do more to engage the wider research community. He also has concerns about the new approach to data privacy, which he sees as problematic not just from a UX perspective, but also for the security risks it brings.
I’ve written about Catalina a few times for SentinelOne, so that’s the best place to go to get a more in-depth or technical view, but there’s no doubt that Apple take macOS security seriously. They genuinely are trying to solve the security problem on their platform. However, there are two fundamental tensions going on with Apple that I feel undermine their efforts.
The first is Apple’s reluctance to admit there’s even a problem. Their marketing efforts demand that they portray Macs as secure and malware-free, but that narrative prevents Apple from sharing intel with and participating in discussions about macOS security with the wider community of macOS malware researchers. Apple are in a unique position in terms of being able to gather telemetry on what’s happening on every Mac in use, but so long as Apple continue to hide threat intel away from other security vendors that could make use of it to defend users with technology that Apple’s own attempts can’t match, there’s always going to be room for bad actors to exploit the gaps between us.
The second tension is that with increasing focus on harvesting and exploiting user data by pretty much everyone — good and bad actors alike — Apple have, I think reluctantly, decided to break their own “rules” about what constitutes good security and good user experience. Specifically, I’m talking about the move now to popping user consent dialogs as a primary security mechanism. Apple once mocked Microsoft for the same behaviour, and as recently as 2013 or so, they were telling developers at WWDC not to use consent dialogs as a substitute for designing truly secure apps. They’ve clearly reversed that decision, perhaps out of concern about liability. After all, if the user grants consent, then it’s no longer Apple’s problem or responsibility. I think it’s the wrong move. I agree with the “old” Apple vision that security should take place at the OS level and without the need for user intervention. Of course, that’s a difficult nut to crack. At SentinelOne, we put in a lot of hard work to make sure our engines can discern the malicious from the benign without disturbing the user or impacting their productivity. Consent dialogs fundamentally offer bad actors the chance to socially engineer their way past the built-in protections, and we know how good they are at doing that.
It seems unlikely that Apple will shift back to its older model of security, though some still hold out hope. For the time being, at any rate, Mac users will be called upon to make more decisions about their systems and the apps running on them.
It may therefore be wise for everyday users to begin going a little deeper into the nuts and bolts of their operating systems, learning how they actually function underneath the slick user interface.
But Macs are enormously complex machines, and beginning to dig around in the guts of an operating system can be a daunting challenge even for people who are highly motivated to learn more.
Stokes appreciates the difficulty involved in grasping the inner workings of macOS more than most. But he suggests that there are two excellent places to begin for those looking to learn:
Macs are still fundamentally built on top of a Unix-like system, and the heart of such systems is the command line, a.k.a. The Terminal. I’d say a great start to understanding any computer (even Windows 10 now) is learning about the command line, what it is, what it can be used for, and how it can lead you to more powerful control than you can get in the everyday GUI world of icons and menus.
Writing scripts is a great way to learn about a system and can lead you down some fun and exciting paths. On macOS you also have the benefit of access to AppleScript, a truly powerful technology that’s really underappreciated. I’ll be talking about that at Objective by the Sea, actually, because people tend not to think of AppleScript from a security angle, even though it’s widely leveraged in adware and malware. Like shell scripting, learning about AppleScript and how you can use it to automate tasks, manipulate other applications, and “bend the OS to your will” is a great way to learn how macOS works under the hood.
While home users may want a better understanding of macOS for personal reasons, there is also an urgent need for increased knowledge in the workplace. There is now a critical cybersecurity skills shortage in the global economy, and the situation is not expected to get better any time soon. With security skills in such high demand, many students and career-changers are looking at the field as an attractive option.
There is no shortage of advice out there for people looking to break into the industry. But Stokes has a unique perspective to offer, because unlike many security professionals, he came to the field from a non-technical background and is almost entirely self-taught. Stokes reflects on the winding road that led to his current work, as well as what he might have done differently:
I’ve always loved exploring things that strike me as “mysterious” or difficult to comprehend, and I love jumping down the rabbit hole to wherever that may lead.
I’m not sure there’s any “one path” or even an ideal path; people come to things differently and bring their own unique skills and background to bear. I think that shapes a lot of both how you learn and what learning path you choose to take. In my own case, I’ve always loved exploring things that strike me as “mysterious” or difficult to comprehend, and I love jumping down the rabbit hole to wherever that may lead. It might start off with something as mundane as an unexpected dialog alert or spotting an unusual process in the Activity Monitor. Where did that come from? What’s behind it? What use is made of it? And so on.
In terms of hindsight, in my own case, if I could go back and start my journey again I’d probably take a more structured approach, try to be more methodical about learning things rather than haring off down blind alleys. It’s a great adventure doing things that way, and fun when you stumble across unexpected finds, but it also wastes a lot of time, so isn’t great for productivity. It’s probably good training for someone who wants to focus on bug hunting and malware research, which is what I’m mostly doing now, so that turned out to be a fortunate stroke of luck, but yeah, maybe not so good for someone that primarily wants to get into something like developing apps!
SecureMac would like to thank Phil Stokes for taking the time to speak with us. To learn more about Phil and his work, follow him on Twitter or stop by the SentinelOne blog, where he writes regularly.
Phil’s presentation for Objective by the Sea 3.0, entitled “Living Off the Land with AppleScript for Attack & Defense”, as well as all of the other presenters’ talks, will be made available via livestream to supporters of the conference’s parent organization. If you would like to support the conference and watch the livestream of the talks, please visit the Objective-See Patreon page.