This week on The Checklist:
- Apple fights mercenary spyware
- Another medical data breach
- What your AirTag is saying
Taking on the mercenaries
There’s a commercial spyware industry that serves governments and law enforcement agencies around the world. We talked a lot about one of the biggest commercial spyware vendors, NSO Group, last year. Their notorious Pegasus spyware was the subject of Checklists 240, 241 and a few other episodes as well.
The makers of commercial spyware — called “mercenary spyware” by Apple — say that they’re just trying to help the authorities fight crime. But reporters and researchers have demonstrated that repressive governments often use it to target journalists, activists, and political opposition figures.
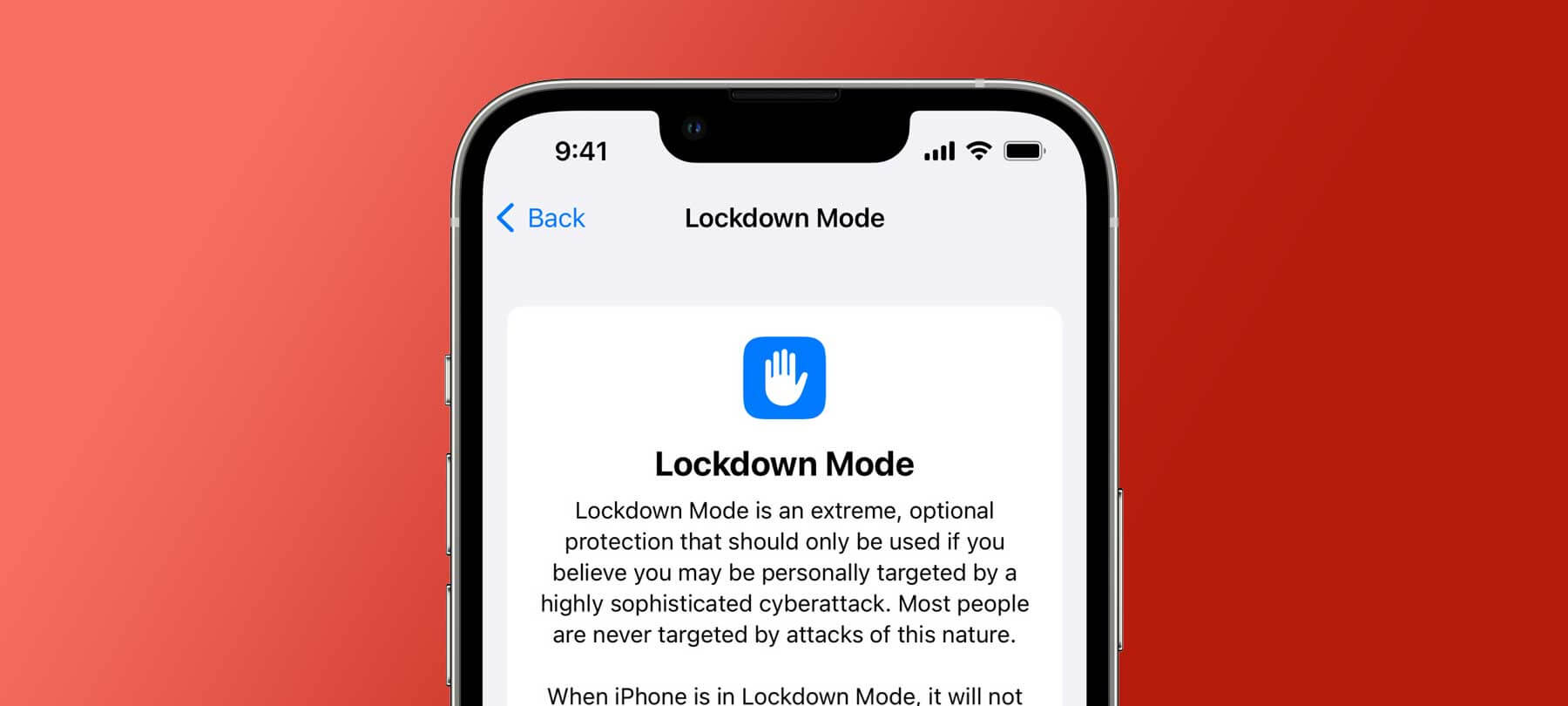
It’s a serious privacy and security issue, which is why Apple is introducing Lockdown Mode in iOS 16, iPadOS 16, and macOS 13 Ventura. According to Cupertino, Lockdown Mode is:
…a groundbreaking security capability that offers specialized additional protection to users who may be at risk of highly targeted cyberattacks from private companies developing state-sponsored mercenary spyware.
How Lockdown Mode works
Lockdown Mode works by taking the radical step of turning your smartphone…back into a regular phone! Apple says that the first version of Lockdown Mode will include the following protections:
Messages: Most message attachment types other than images are blocked. Some features, like link previews, are disabled.
Web browsing: Certain complex web technologies, like just-in-time (JIT) JavaScript compilation, are disabled unless the user excludes a trusted site from Lockdown Mode.
Apple services: Incoming invitations and service requests, including FaceTime calls, are blocked if the user has not previously sent the initiator a call or request.
Wired connections with a computer or accessory are blocked when an iPhone is locked.
Configuration profiles cannot be installed, and the device cannot enroll into mobile device management (MDM), while Lockdown Mode is turned on.
Of course, Lockdown Mode isn’t a panacea. iPhones still have to connect to cellular networks, and will broadcast other information that can be used against their owners. But for the high-risk individuals likely to be targeted by mercenary spyware, Lockdown Mode is a huge safety and privacy enhancement.
Medical debt, identity theft, and you
1.9 million patients were affected by a cyber incident at a medical debt collection firm, according to a recent piece in TechCrunch. TechCrunch says that the incident was actually a ransomware attack that also resulted in the theft of:
…patient names, addresses, their outstanding balance and information relating to their account…in “some cases” dates of birth, Social Security numbers and health insurance and medical treatment information were also taken by the attackers.
We’ve talked before about healthcare data privacy, as well as how data breaches at medical providers can lead to identity theft. But what’s noteworthy about this incident is that the victims of the breach didn’t even have a relationship with the organization that was attacked.
Sure, they’d given their personal information to their healthcare providers. To doctors and hospitals, insurers and clinics. But not to “Professional Finance Company,” the Colorado debt collection firm that suffered the breach.
The takeaway from this data breach is that you never really know who has your information — because the people managing your data may have shared it with third parties. For this reason, it’s important to remain vigilant, and to make a practice of regularly checking your financial accounts and credit reports for signs of suspicious activity.
The sounds of AirTag
If you’ve listened to The Checklist for a while, you know that AirTags are Apple’s personal tracking devices for stuff … and also a privacy and security nightmare.
The good news is that Apple has listened to concerns from the public and the security community. The company has taken steps to make AirTag safer, and to fight back against misuse by stalkers and other criminals.
AirTags make a number of sounds that let you know what’s going on with them, including alerts that tell you when an unknown AirTag is traveling with you. These are:
- Welcome and Battery Connected
- Setup Complete
- Find My
- Moving With You
- Locate AirTag Moving With You
To hear these sounds, listen to segment three of this week’s Checklist via the player below — or check out Apple’s video demo on YouTube.
Do you have a question for The Checklist, or for the Mac security experts at SecureMac? Drop us a line and let us know — we love answering listener questions on the podcast!