New Mac Malware Knows When You’re Watching
Security researchers at Intego have discovered a new form of Mac malware—one that shows some surprisingly sneaky behaviour aimed at evading detection by antivirus software and human malware hunters alike.
Dubbed “CrescentCore”, this clever little program is yet another example of what developers have been saying for a while now: macOS malware is on the rise…and it’s getting more and more sophisticated.
What does it look like?
CrescentCore is a Trojan. It’s disguised as an Adobe Flash Player installer, which unsuspecting users would download onto their system as a .dmg file—the same sort of disk image file format that a legitimate app might use.
What does it do?
Here’s where things get interesting.
Once downloaded, CrescentCore checks to see if it’s running inside a virtual machine, or VM. VMs are virtualized operating systems running on a system’s actual operating system (sort of like an OS within an OS).
So why does CrescentCore want to know if it’s in a VM?
Because virtual machines are used by security researchers to study malware safely (as opposed to just downloading malware onto their computers, which would be a very bad idea).
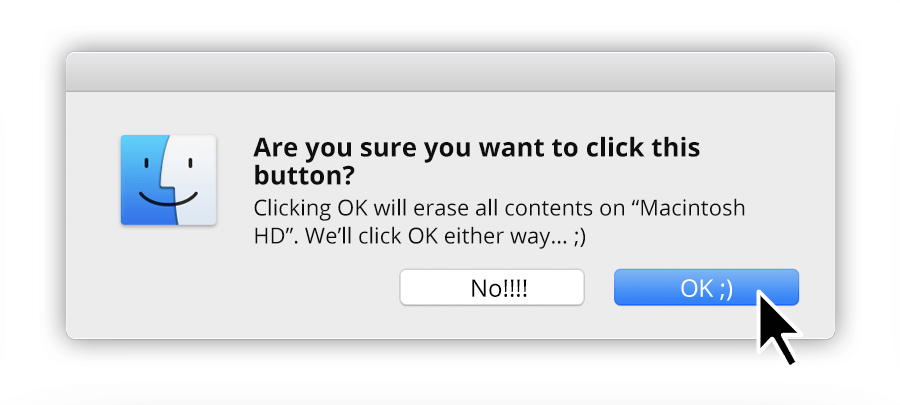
In other words, CrescentCore wants to know if it’s being watched!
If the program discovers that it’s in a VM (and thus might be seen by a security analyst), it simply won’t run.
CrescentCore also determines whether or not the user’s system is running third-party antivirus software—i.e., another possible means of detection. If it sees that the system is protected, once again, it’s “abort mission” time.
What if you’re not protected?
But what if the malware figures out that it’s on a system that a.) isn’t a VM and b.) isn’t protected by antivirus software?
Well, then it’s game on.
The Trojan proceeds to install a LaunchAgent, which gives the malware a foothold in the OS and lets it run scripts that control system processes, launch itself again and again, and generally make itself very difficult to get rid of.
The researchers who discovered CrescentCore say they’ve seen other variants of the Trojan which install unwanted applications or unsafe Safari extensions.
How to keep yourself safe from CrescentCore
Here are a few things you can do to make sure you aren’t affected by CrescentCore or similar malware:
1) Be skeptical.
CrescentCore showed up on some predictably sketchy websites, but also in high-ranking Google search results. And the installer .dmg itself? Signed with genuine Apple Developer IDs.
We’re going to be seeing more malware that directly targets macOS—and it’s going to keep getting better.
So as a general rule, don’t make the mistake of assuming that because something looks legit, it’s safe. Be careful where you browse, and never download a program onto your machine unless you’re absolutely sure of the source.
2) Watch out for Flash
If you’ve followed the Checklist podcast for a while, you know that bogus Adobe Flash Player updaters have been used by malware authors before.
The good news is that you won’t have to worry about this much longer—Adobe itself is phasing out support for Flash at some point in 2020, and most of the web has moved away from it already.
Until then, either use a browser with a built-in Flash player (like Firefox) or just don’t run Flash on your computer at all.
3) Get protected
The idea that “Macs don’t get viruses” is badly out of date. If you’re running a macOS system without using a good antivirus program, you may be vulnerable.
Products like SecureMac’s MacScan offer reliable protection and frequent updates—which is exactly why the malware authors behind CrescentCore didn’t even try to run their program if third-party AV was active.
If you want to protect your Mac today, you can download MacScan 3 as a free trial.
It’s a given that bad actors will continue to develop new and increasingly tricky malware targeting macOS users. At SecureMac, we believe that knowledge is the first line of defense—so follow us on Facebook or Twitter to receive breaking news and regular updates on Mac security. And be sure to tune in to our weekly Checklist podcast for an in-depth discussion of all things cybersecurity for Mac and iOS users.